The average citizen has security concerns and can benefit from an understanding of the concepts of surveillance countermeasures that enhance personal protection. However, the application of surveillance countermeasures without a sound perspective regarding the threat-specific surveillance techniques they are intended to defeat can be counterproductive, and potentially dangerous. For this reason, the practitioner of surveillance countermeasures must think like a surveillance operator in order to anticipate how an operator would act based on specific circumstances.
Stop Procrastinating
Life can have a habit of getting in the way, as we have all seen in the past couple of years but looking inwards at the goals you set out for yourself, is it life that has stopped you from achieving them or is it barriers put up by yourself?
I have always liked to set goals for myself and work towards achieving them. Still, when life comes on top, and with a heavy workload, it is very easy to push things to the right and look to complete these goals later…….the only problem with this is whether the actual task or goal you have set yourself gets completed or gets forgone completely?
I have learned that the more you put things off, the more significant the task pile can become, and you can quite literally make a mountain out of a molehill where in the end, you accomplish nothing.
Cyber Security Fundamentals – Deepfakes and Impersonation
Luckily when you make the pickup, you confirm with them. They’re surprised at the request as they don’t recall calling, and so you don’t make the route change.
Later investigation reveals that the call was made from a spoofed phone, using a real-time generated video and audio stream of the principal mapped to the live movements of some unknown adversary.
Knowing When to Quit
With time no longer on his side he begins to bounce from one team to another, often going from being the star to the second unit, maybe begins playing a different position, begins making errors on routine plays, getting fewer at bats, doesn’t carry the ball as often, not called upon when the score is tight. Many former stars “hang around one season too long.” Everyone but the athlete sees what he doesn’t, namely that it’s time to retire!
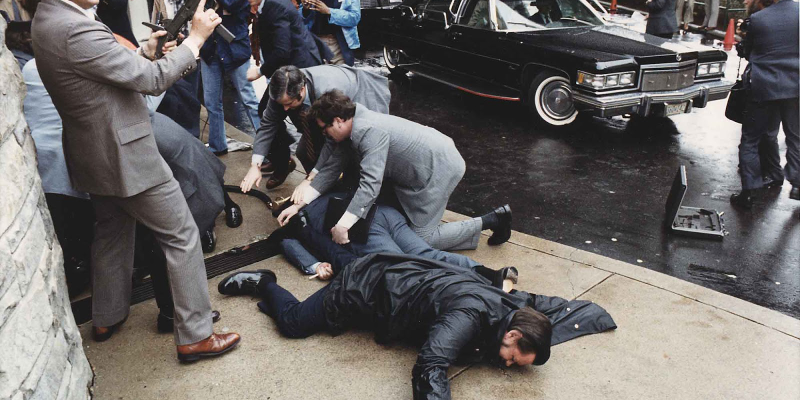
When Push Comes to Shove – Combat Principles for Executive Protection
Although prevention is the primary goal, there are times where proactive, effective physical intervention may be required. This is not to be confused with arrest and control techniques used in other related security fields. Those techniques have merit, but the goal of this article is to highlight combat principles agents can apply when cover and evacuation is not an option, and the threat is imminent.
Navigating the Complexities of Wi-Fi Installations
Wireless applications present unique challenges. By carefully planning and understanding potential obstacles, installers can avoid common pitfalls and ensure a more reliable Wi-Fi security setup.
Operating as a Commercial Sniper The Myths and Facts
To start with, let’s kill a central myth right off the bat. And that myth is that jobs for commercially employed snipers are widely available and accessible. That is not true. You will not do a sniper course and then be hired as a sniper in a war zone. You will not find any companies that are advertising such jobs. If they are, then I’d be dubious.
LIFE & WORK SKILLS: CONFLICT MANAGEMENT FOR PROTECTORS
Pop quiz: What do you think is greater, the number of executive protection agents who have been fired because their client got killed? Or the number that got fired because a client’s wife/manager/trusted advisor straight-up didn’t like them? I think anyone who has been around the industry longer than five minutes probably knows the answer to that question.
Empowering Strong Women Through Training
Talented and motivated professionals understand this and continuously train and educate themselves in current methods. They also take note of changing strategies to be most effective in their pursuit for the opportunity that will set them apart from other men, and a small number of women, in the industry.
Having “Opinions” Can Make or Break You
We live in a time where people’s opinions invade, dictate, and in some instances, ruin lives. Businesses opinions sell merchandise. Financial and political people tell you where to invest your money or who you should vote for. Opinions are very personal, varying from person to person, but they all have in common that they are nothing but a singular view of a singular event or action.
Behavioral Analysis Part 2
Following on from what was discussed, in order to deeply understand how these incidents occur, we need to understand the differences between the radicalization and recruitment processes that enlist Homegrown Violent Extremists and Active Killer incidents.
Size vs.Skills-a.k.a: The Unfair Advantage
However, this lesson sticks out because I still think about it and even use it to this day. My dad told me that every person on this planet has an ‘Unfair Advantage.’ Something God-given that a person does exceptionally well or better than anyone else. He told me that some people could naturally run fast or dunk a basketball without even really trying. Some can figure out complex equations in their heads like Einstein or even maintain a full head of hair well into their old age. Whatever gift you possessed that you did better than anyone else was your unfair advantage.
Security and Technical Debt Collection
Technical debt is what you are adding to every time you choose an easy or quick solution now, rather than looking at longer-term strategies. It is the technical expression of ‘failing to plan is planning to fail.’ And it has consequences.
Protective Tactics for Attending High-Risk Meetings
Arranging and attending high-risk meetings is an easy way to set someone up for kidnapping, assassination, sexual assault or robbery. Because of this, meetings in high-risk situations can be extremely dangerous and should always be treated with caution whether you are attending for personal business reasons or with a client.
Will Manners still Maketh the Man?
When a gentleman offers his hand—gloved or ungloved—a lady does not recoil and yell, “What are you, crazy?” This is a handshake, and a lady knows it poses her no threat. If she must sanitize immediately afterward, she will do so discreetly.
Keeping Your Edge: Raising Your Profile
This is not so much by the overt actions we take in close proximity to the Protectee, but by the intentional maneuvering of chess pieces behind the scenes, in the form of risk analysis, advance-work and logistics. With the exception of very high profile, or high threat assignments, our default state could be described in many cases as, invisible. This mindset has successfully shepherded many throughout the profession, being passed on from generation to generation to the benifit of the craft.
The Anatomy of a Bank Robbery
Even as banks deal with the fallout of the pandemic, bank robberies on the whole since Covid-19 are actually down. And while banks have always denied access to people wearing masks, the challenge posed by mask wearing during the pandemic has invited a greater security risk to banks, according to Paul Benda, Senior Vice President for Risk and Cybersecurity Policy at the American Bankers Association.
The Threat Posed by Fixated Individuals
The woman, who claimed she was engaged to Prince Andrew managed to persuade the security officers at the Royal Lodge to pay for her taxi fare. She then spent 20 minutes wandering around the Royal gardens before entering the home of Prince Andrew, Duke of York, where she was finally detained, and subsequently sectioned under the Mental Health Act.
OSINT ON-THE-GO
We live in a fast-moving world. Technology is evolving faster than we are. Is all the technology around us causing us to think that time is ticking faster?
Time does indeed seem to have become more precious nowadays. And many people often do say, “I can’t find the time to do it, the days are just passing too fast.”
But think back to not so long ago, especially us “oldies” on the circuit…
Conspiracy Theories Can Increase the Risk of Targeted Violence
A social climate of uncertainty provides fertile ground for conspiracy theories. Pandemics, for example, are predictably unpredictable—no one can say with certainty when one might begin, when it would end, or how long it might last. Combined with political and economic instability, a public health crisis like COVID-19 is rocket fuel for conspiracies. Under conditions of uncertainty, any information, even rumors, that helps direct negative emotions toward a specific target is psychologically comforting—it helps people manage their fear and anxiety. What if that target is your principal, a powerful business person, political figure, celebrity or high-wealth individual, who unwittingly becomes a central figure in an elaborate conspiracy theory due to their publically-known views, financial activities or associations?