When discussing executive protection topics with somebody not working in this field of expertise, the threats to the principal are often expected to come from rare incidents such as stalkers, snipers, explosions and so on. As professionals we know that the most significant and likely threats come from car accidents and health issues, then, next in line are serious fire emergencies. Don’t just take my word for it, a quick look at the statistics show just how frequent and deadly fires are in US.
Foot Steps: Episode 3 – Devon Taitt
I believe everyone should spend at least a year working the clubs on the weekends. You will develop your self-awareness, situational awareness, verbal and nonverbal communication skills, and overall confidence. It’s controlled chaos. The perfect training ground.
Freedom or Security?
According to Paine, if twenty persons, all strangers to each other, found themselves in a previously uninhabited country, each individual’s will was his natural right. He had the freedom and liberty to do as he pleased, even invading the sovereignty of his neighbors. It would then occur to each sovereign individual that if he united with his neighbor for mutual protection he would increase his personal security. But to do that he would have to sacrifice certain degrees of his natural rights. The compromising of individual rights resulted in rights of “compact” or as our legislative laws were defined as “civil rights”.
At the Point of Crisis
Many of you will have seen the photo of the Dallas shooter outside of the Federal Building. Now ask yourself if this was your Office, School, or House of Worship how prepared would your company or institution be to recognize the signs of trouble as those Federal Officers did and deny access and ultimately defeat the shooter?
Industry Standards Are They Out the Door?
There is an age-old adage, which states that in this world ‘you get what you pay for’ and nowhere is this truer than in the Protection Industry.
As someone who runs their own security company, I know this only too well. However, this lesson was firmly reinforced after I rashly agreed to take on a job that my gut had warned me to avoid.
Counter-Ambush Tactics for Security Professionals – Part 2
The first two of these tenets involve soft skills which are sometimes referred to as Protective Intelligence (PI) and include situational and tactical awareness skills (route analysis and surveillance detection). The third tenet, Defend, requires hard skills such as the use of firearms and security driving. These hard skills may be required if we were unable to prevent or avoid an attack, and we end up in a situation where we have to survive an ambush. Continuing where we left off in Part One, we will finish covering some of the soft skills involved in Protective Intelligence and then move on to discuss the hard skills.
Creating a Safe Environment – What is a ‘Protective Bubble?’
If you’ve spent enough time around executive protection professionals, you’re no doubt familiar with the concept of creating a bubble around a protectee. It seems simple enough, right? Create the protocols, vet those with which the protectee interacts, and stringently direct the protectee’s activities without deviation.
In reality, of course, creating a safe environment for those elected officials, business leaders and celebrities who require protection by statute, board decree, or simply because they attract unwanted attention is an enormously challenging task that requires tremendous flexibility and innovation from those responsible. Let’s be honest — while many people who require such protection for their own safety understand and appreciate the necessity, they, including some past and current U.S. Presidents, are not always cooperative when faced with security limitations.
Protecting the Principal in a Pandemic
From an operational perspective, CPs need to go back to fundamentals and apply the golden rules of protection planning and risk assessments to medical scenarios. For instance, from a strategy perspective, many HNW bought ventilators only to later discover that they would never be delivered due to shortage. So, it’s important to think how do we improve our planning and strategy from the outset to account for the unexpected? Scenarios and risks should be assessed as always in a well thought out threat matrix.
Keeping Your Edge – Measured Responses in Tour Security (Part II)
These challenges can take the form of unintentional harm coming by way of a prop, stage equipment, or something as simple as a slip and fall caused by a long dress and high heels.
Whenever we can, we as Protectors must try and anticipate, correcting or counteracting the occurrences that can cause this harm. This is usually done during the Site Advance at which time we do a walk-thru of the areas that the VIP will be visiting, in this scenario, the stage. It is at that time we will perform a visual inspection of the stage and the props, go hands-on with items the Protectee might come into contact with, such as the guard railing, and enlist the help of experts to answer questions that are beyond our realm of expertise, such as how the overhead lights are connected to the scaffolding.
The Fallacy of the Individual Bodyguard
It was the height of British military and government involvement in the ill-fated NATO-led effort to crush the Taliban, and Kabul was inundated with people needing close protection services. From diplomats attempting to build infrastructure and civil institutions to corporate honchos sniffing out potential business opportunities, there was no shortage of clients for security firms to pitch. As my conversation with the in-country manager progressed, I broached the subject of IBGs – individual bodyguards. I told him in no uncertain terms that the idea of having an individual effectively carry out the functions of a close protection team was utter and absolute flannel. His response: “Maybe, Bob. But it brings in the dollars!”
Defining Professionalism in the Personal Protection Industry
Not because there is less work out there, in fact, the opposite is probably true. With global threat levels at an all-time high, there is more work in the security industry now than there ever has been and the security industry is booming, but it’s harder to find work because there are now thousands more so-called ‘qualified’ CPOs chasing after every position. It is a fact that most licensed operators have never actually done a day’s close protection work in their lives. At the time of writing this article, there are over 14,000 valid, UK, CP licences. Yes, over fourteen thousand people in the UK currently have a license to operate as a Close Protection Officer.
Counter-Ambush Tactics for Security Professionals – Part 1
By far the best method to accomplish this goal is to adopt a predictive, preventative strategy for protecting clients based on the tenets of Detect, Deter, and Defend. To effectively employ these tenets, we need some very specific soft and hard skills. In the protective operations world, the “soft” skills are sometimes referred to as Protective Intelligence (PI) while in other security disciplines they are referred to as situational and tactical awareness skills. If we are unable to prevent or avoid an attack, we need to have some expertise in specific “hard” skills such as use of firearms and security driving so that we can survive an ambush.
Hero bodyguard throws himself in front of client after motorbike hitman opens fire
A man on a motorbike cruises into the hotel grounds and pulls up close behind the SUV when the bodyguard places himself between the woman and the attacker.
Introduction to Cybersecurity
Cybersecurity is often seen as a niche area which requires a lot of specialist knowledge to apply. This is partly true – in order to configure a web application firewall someone needs to understand how to work with the technology at a very low level. What is often missed, as the technologists take over, is that cyber is still security and the same fundamental principles apply to designing and building effective protections.
Church Security – The Five R’s of Venue Protection
People go to church for all kinds of reasons but almost no one goes to find trouble. The ones that do go for that purpose are the reason your church has a security team or ministry. Unfortunately, over the last twenty years “Trouble” has been finding its way into church for the simple reason that for the most part, we welcome it. Church is still the place that welcomes anyone in any condition to come to find help.
A Formula for Surviving School Shootings
No one wants to think about someone opening fire at their child’s school and I’m no exception. That’s why I’ve harnessed the knowledge and experience I’ve gleaned through two decades of Special Forces soldiering to advocate for a formula for surviving school shootings: Speed + Distance = Survival. When a shooter opens fire, you have one chance, and one chance only to get it right.
The security challenges of Bleisure Travel
The security challenges of Bleisure Travel (combining business travel with leisure time), is a challenging prospect for those working in security, risk and business continuity roles. Bleisure is a growing trend, with just under half of all business travellers now routinely extending their trips by a couple days.
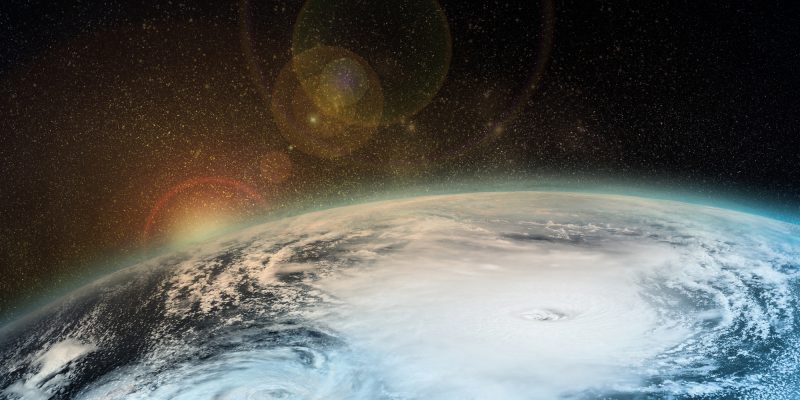
Preparing for the 2018 Atlantic Hurricane Season
As the 2018 Atlantic hurricane season approaches, concerns exist of a repeat of the destruction experienced last year. The responsibility of security, risk and business continuity teams is a complex one. You are your organization’s first line of defense against any and all threats to operational continuity and people safety. How should you go about reducing your exposure?
Are These The Top 5 Home Security Technologies Available?
Endless new offerings on the market may seem overwhelming and daunting to customers when choosing the most efficient security system for their home’s needs.
We have done the late night research and have narrowed down the top 5 new home technologies for all homeowners, to assist with your decision making.
Safety Tips for Travellers at the 2018 Russia World Cup
By staying aware of threats, travellers and security teams can thoroughly prepare themselves for the risks they face at the 2018 Russia World Cup. Whether this means having a greater awareness and understanding of the threat landscape, or actually vetting every step of the journey, working proactively to mitigate the risks is by the far the best approach you can take.