Talented and motivated professionals understand this and continuously train and educate themselves in current methods. They also take note of changing strategies to be most effective in their pursuit for the opportunity that will set them apart from other men, and a small number of women, in the industry.
The Threat Posed by Fixated Individuals
The woman, who claimed she was engaged to Prince Andrew managed to persuade the security officers at the Royal Lodge to pay for her taxi fare. She then spent 20 minutes wandering around the Royal gardens before entering the home of Prince Andrew, Duke of York, where she was finally detained, and subsequently sectioned under the Mental Health Act.
Establishing Your Career Path in Close Protection
Now, to make it clear the commercial close protection industry is a very difficult industry for most people to enter, mainly due to the fact it is a very small and clique world where doors usually open for people if they know the right people. So, to start with, networking is a valuable key to opening the doors.
My personal experience and opinions comes from working over 30 years’ within the security, close protection and risk management industry in various Central/East/West African countries, Europe and Asia in operational and management positions.
Importance of Continued Combatives Training
Within the industry, it’s been long debated whether or not martial arts training is essential to an agent. And if so, what style? In my opinion, the short answer is, of course, it’s essential. In this industry, we voluntarily take on responsibility for someone else’s defense. This implies that we should have an adept ability to protect ourselves proficiently.
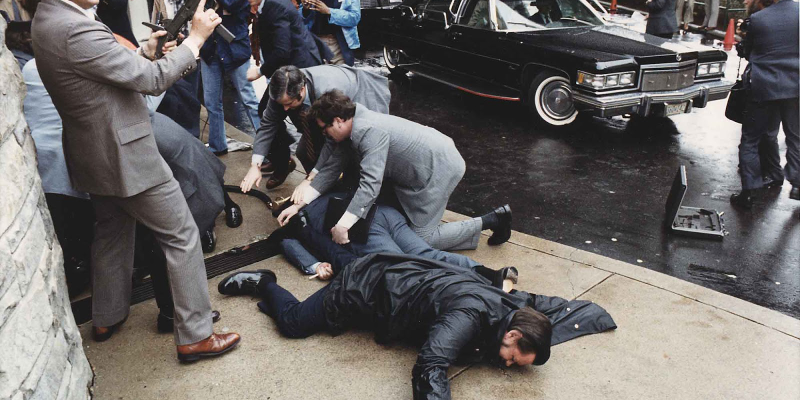
Formations, Body Cover, & Professional Distance
The key words to remember when escorting a client on foot are flexibility and adaptability. You must be flexible enough to constantly adapt your formations to the environment you are working in, the threat level, and the manpower available. Whatever formation you are using will only be as good as the people you are using in your team. You must select your team carefully. Vet all potential members of your team before you employ them, even if you have known them for a while. Many people can talk the business, but when they get on operations, they are useless. When time allows, conduct rehearsals of all your team drills so in the event of an emergency, everyone knows what to do and what everyone else is doing.
Memorial day, we need it more now, and we need to talk about it.
As the world comes to grips with the effects of COVID-19, it has changing how we live and work in ways we would not have thought possible even months ago. Today’s new normal for businesses includes work-from-home difficulties, many simultaneously sick workers, disrupted supply chains, cash crunches, uncertain compliance obligations, and the mechanics of applying for new government programs. But that gives us time to reflect on other important matters, Memorial Day and the value we should instil.
The Importance of Emotional Control in the Workplace
If you are a service provider, you must always have in mind that people you employ and place with clients are the people who represent your brand. Their mistakes will harm you more than it will harm them. Most companies are losing contracts due to the toxic or unprofessional behaviour of their operatives.
Behind the Veil
Behind any large delivery service are logistics personnel, without these individuals nothing would move and production would grind to a halt. Likewise, backing any police force, there are a group of emergency dispatchers that help send, coordinate, and give real time information to responding officers. With airline pilots, there are a team of air traffic controllers that convey critical information to the pilot for a safe flight. And in the same vein, behind Executive Protection Specialist, there may exist a caring spouse, or partner.
The One Percent
Cybersecurity provider NTT Security reports that five countries are the most common sources to 50 percent of global cyberattacks (Figure 2). Akamai states that two-thirds of Distributed Denial of Service (DDoS) cyberattacks originate in ten countries. Symantec, another provider, adds 13 more countries for a total of 23 countries, which are homes to the worst cyber offenders and who are responsible for two-thirds of all malicious internet activity.
Preparedness & Perseverance
. To prepare is to, make (something) ready for use or consideration, to persevere, is to continue in a course of action even in the face of difficulty or with little or no prospect of success. Among the many skill sets we must attain, practice, and master over time, preparedness and perseverance are two less talked about traits of a solid EP practitioner. There are many reasons why the focus on these skills are over shadowed by wrist locks, positioning, being the body man, fancy martial arts, and firearms. What’s a significant reason you ask? Well, in my opinion it’s because there is no immediate gratification, or “look at me” moment(s). There are plenty of instances where all of the before mentioned skills are useful, however, how and when they can be used start with being prepared.
Venezuelan Gold-Trafficking
The gold business in general is a haven for scammers, money launderers, traffickers, criminals and terrorists. It is an area rife for the services of a protection specialist since the coupling of unsuspecting investors, with sometimes, greedy buyers can lead to a lot of trouble and loss of money, property, and even lives.
Bodyguard Saves Japanese PM from Pipe Bomb Attack
A bodyguard has been hailed as a hero for his quick-thinking actions during a suspected pipe-bomb attack on Japanese Prime Minister Fumio Kishida. Video footage captured the bodyguard kicking away a metal object as it landed near Kishida
before positioning himself between the Prime Minister and the device, shielding him with a collapsible, handheld ballistics shield.
So, you want to be a Hostile Environment Security Adviser?
“War correspondents” I mistakenly thought, were hand-picked for their skills set, fitness, mental toughness, awareness, and clean living. But no, what I found instead were individuals with many issues ranging from drug and alcohol problems to PTSD episodes to fundamental fitness concerns… the list goes on.
Training for When Time is Life
The 21-foot rule has long been an established firearm training standard. Simply put, it means an average man can close 21feet in 1.5 seconds, as we look at the below data of attacks on law enforcement officers the previous standard far from reflects the reality of the dynamic encounters in both distance and timing in enhancing your ability to prevail in a violent close quarter firearm encounter.
Defining Professionalism in the Personal Protection Industry
With global threat levels at an all-time high, there is more work in the security industry now than there ever has been and the security industry is booming, but it’s harder to find work because there are now thousands more so-called ‘qualified’ CPOs chasing after every position.
Tips and hints for finding work in the personal protection industry
One of the most important things you should do is to decide very early in your career which environment and in which speciality you wish to work. You cannot do anything significant unless you make this fundamental decision.
Gap Training, What Most Practitioners Overlook
With 30 years of experience as a sailor, soldier, police officer/EMT, and security provider and trainer I have come up with some pretty clear ideas about what medical first response is for the average security provider. This is not meant to deter anyone from obtaining their EMT or Paramedic certifications or from persons with higher levels of training from providing that service.
Regaining balance after a threatening encounter
There’s no denying that security and close protection work is mentally and emotionally demanding. Life-threatening situations, exposure to graphic scenes, distressed individuals, and violent perpetrators as well as the occupational stressors such as unsocial working hours and being away from home mean you need to be operating at peak levels of resilience.
Situational Awareness Skill or Instinct?
Situational Awareness is “the perception of the elements in the environment within a volume of time and space, the comprehension of their meaning and the projection of their status in the near future”.
Are you a cut above your competition?
For many years good friends of ours in the close protection and military sectors have said to us that what is really needed whilst transporting their clients and personnel is the ability to carry out an emergency rescue immediately following a vehicle incident whether it is accidental or a deliberate attack on their vehicles, some of which, may be armored presenting even further rescue difficulties.





![That of the person who has a degree in Psychology and has also spent many hours studying behaviours.[Fragment] I would like to combine my two educational backgrounds and discuss how specific behaviours can negatively affect the security industry.](https://circuit-magazine.com/wp-content/uploads/2023/12/pexels-andrew-neel-2312369-750x400.jpg)