Pop quiz: What do you think is greater, the number of executive protection agents who have been fired because their client got killed? Or the number that got fired because a client’s wife/manager/trusted advisor straight-up didn’t like them? I think anyone who has been around the industry longer than five minutes probably knows the answer to that question.
The Anatomy of a Bank Robbery
Even as banks deal with the fallout of the pandemic, bank robberies on the whole since Covid-19 are actually down. And while banks have always denied access to people wearing masks, the challenge posed by mask wearing during the pandemic has invited a greater security risk to banks, according to Paul Benda, Senior Vice President for Risk and Cybersecurity Policy at the American Bankers Association.
Importance of Continued Combatives Training
Within the industry, it’s been long debated whether or not martial arts training is essential to an agent. And if so, what style? In my opinion, the short answer is, of course, it’s essential. In this industry, we voluntarily take on responsibility for someone else’s defense. This implies that we should have an adept ability to protect ourselves proficiently.
The Importance of Emotional Control in the Workplace
If you are a service provider, you must always have in mind that people you employ and place with clients are the people who represent your brand. Their mistakes will harm you more than it will harm them. Most companies are losing contracts due to the toxic or unprofessional behaviour of their operatives.
Keeping Your Edge: Building a Solid Foundation
Longevity, consistency and remaining relevant are some primary goals of all protectors. These factors are important when establishing a new contract and providing services for a new client. But what is equally important is the mindset that goes into those first days and weeks on the assignment. As such, I wanted to get the personal perspective of Vantrell Wilson, a close protection agent who I have trained with and worked alongside of for years now.
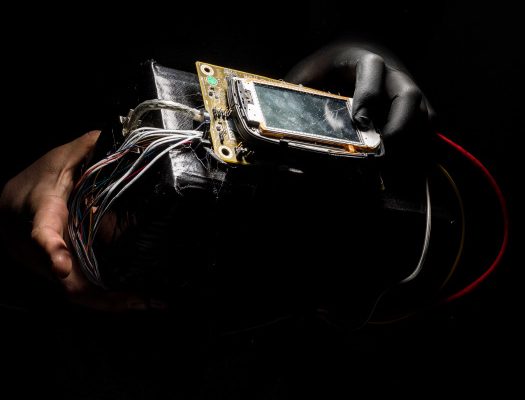
Kidnap & Ransom – Part two
In the previous issue we walked through what happens in the first hours after a kidnapping, we considered the critical factors relating to the initial contact, and we took a close look at the role of the communicator (see Issue 49). Now, we’re going to move on and look at the financial implications of ransom demands and what factors might impact it.
Fit for Duty: Health & Wellness as Crucial Daily Hygiene…
The only thing consistent about protective services and extensive travel is that it is consistently inconsistent. The hours are often long, we are up before everyone else and go to bed after everyone else. If your client is a business executive with global responsibility it is always 9:00 AM – 5:00 PM somewhere in the world. So, often your sleeping and eating patterns can become significantly altered. By the time we start or end our day, many times the quality eating establishments may not be open or are already closed.
Tactical Firearms: Pistol Grip Shotguns
These days a lot of people’s opinions seem to be 3rd hand or YouTube based which can be concerning… For me pistol grip shotguns are very effective and versatile weapons if used properly. Shotguns with stocks are easier to use and are more controllable with hotter magnum loads but lack the maneuverability of a pistol grip shotgun.
Meta Fires Security Guards for Hijacking User Accounts
Meta Platforms Inc. has fired or disciplined more than two dozen employees and contractors over the last year whom it accused of improperly taking over user accounts, in some cases allegedly for bribes, according to people familiar with the matter and documents viewed by The Wall Street Journal.
How did Russian woman whose family had links to the Kremlin get a role in an British security body?
Anastasia Spiridonova, 23, who speaks six languages and is described by several colleagues as ‘exceptionally charming’, is connected to the Putin regime through members of her family. Her grandfather was an MP in Putin’s United Russia party, while her mother Marina worked at the Kremlin in a department running resort hotels and presidential retreats around Russia.
The eX-military Factor
I am the son of a soldier, I have a very high regard for the British Army, which in my opinion has been the best in the world since the days of Oliver Cromwell, who created the first People’s Army. Even in the days of conscription, the British Army and its personnel acquitted themselves with distinction in Malaya and Korea. In very difficult circumstances (isn’t all conflict difficult?) they continue to do the bidding of this nation’s rulers across the world in a way that is reflective of the society from which they have come.
Staffing an International Team
When it comes to staffing an international team, I have five major considerations I look for in the team’s composition: Operational Capability, Operational Chemistry, Operational Relevance, Operational Flexibility and Operational Capacity.
Residential Security
Just because someone has a security or private investigators license it does not mean they are competent or not working with the criminals. What a lot of people forget when hiring security personnel is that you get what you pay for.
McDonaldization of Close Personal Protection
The process of McDonaldization takes a task and breaks it down into smaller tasks. This is repeated until all tasks have been broken down to the smallest possible level. The resulting tasks are then rationalized to find the single most efficient method for completing each task. All other methods are then deemed inefficient and discarded.
YouTube Should be Part of Your Social Media Strategy
YouTube is the number two search engine right behind Google (go figure). Everyday 3 BILLION VIDEOS are viewed on YouTube everyday. Why? For me personally and I’m sure thousands of others would rather find a video on how-to fix a widget then read pages of text on a web page.
The Great Firewall of China
From microblogs to what Google and Amazon says, China knows full well that unlimited, unaccountable and unsubstantiated news reports on the nation is simply not in its best interests, or pointedly its cultural interest! That may also mean news reports that are factually correct.
Working with your dissertation supervisor
A dissertation or research project is normally par for the course on degree programmes. In my experience, it is a source of anxiety for many students and I’m in no doubt that this one module can act as a barrier to undertaking a University degree course.
Journalists Covering The Recent Hurricanes
Over the past few days, we’ve all watched journalists behaving like irresponsible children foolishly “braving” the raw elements when a handful of very responsible ones reported from hard cover still managing to show the devastation behind them. My problem with the former…it sets a scene for the future behaviour to continue with the competitiveness of […]
Behavioral Analysis Part 1
Many people spending more time online this past year due to COVID-19 lockdown and isolation has created limited options of socialization, forcing people to a record amount of screen time on the internet and social media. Much more than ever before.
Precious Principals – The Challenges of Protecting Children
My principals’ ages have also ranged from 4 to 65 years old. Amongst them all, I personally believe the most challenging principals are children. For me, the role of a bodyguard caring for a minor is all about balance, judgment, adaptation and a crystal-clear understanding of the parents’ wishes.



![That of the person who has a degree in Psychology and has also spent many hours studying behaviours.[Fragment] I would like to combine my two educational backgrounds and discuss how specific behaviours can negatively affect the security industry.](https://circuit-magazine.com/wp-content/uploads/2023/12/pexels-andrew-neel-2312369-750x400.jpg)