Arranging and attending high-risk meetings is an easy way to set someone up for kidnapping, assassination, sexual assault or robbery. Because of this, meetings in high-risk situations can be extremely dangerous and should always be treated with caution whether you are attending for personal business reasons or with a client.
Social Media Engineering
Take just one example the conspiracy theories around 5G were quickly re-tailored to incorporate Bill Gates and George Soros as targets, and were effective enough that there were arson attacks against 5G infrastructure. In other words, a few memes and videos, along with the use of these techniques (whether deliberate, or accidental, but there is strong evidence of deliberate action) were enough to cause homegrown domestic terrorism attacks on UK soil.
A Deeper Understanding
a PoC service is like any other client server system that you use. Take Skype as an example that many people will be familiar with. This is what is commonly referred to as a ‘client-server’ application. The Skype app sits on you phone, tablet, laptop or desktop and is in constant communication with the Skype servers out there in the cloud.
Protecting Journalists
Personal safety and security is something many take for granted especially in Europe and the US, but these days there are extremists on all political sides, from all religious backgrounds. So, if you or your client are voicing your opinions on any form of media, especially if you know your views may upset or offend others, then you need to think about your security as well as that of your family’s and colleagues.
Residential Security
Just because someone has a security or private investigators license it does not mean they are competent or not working with the criminals. What a lot of people forget when hiring security personnel is that you get what you pay for.
The Key Elements of Counter Surveillance
Counter Surveillance is defined as the actions that a person (or team) carries out, in order to detect that a person (Principal) is under surveillance and to identify the composition and makeup of a hostile surveillance team.
In this article, Pete Jenkins talks through the key principles of a counter-surveillance operation.
Commercial Security Courses
Having dug around in the last year to see what’s going on with security training courses at home and overseas, it would appear that there is a gap between what’s acceptable, to what’s a complete rip off, and that gap is as wide as the Grand Canyon.
Protective Surveillance
With each client, the situation and threat level will vary, as will their requirements and appetite. When it comes to security there are a myriad of options available, often (and hopefully) with multiple, complementary components working together in harmony. One weapon in the personal protection armory is Protective Surveillance. This article attempts to provide a comprehensive overview of a service that has multiple benefits, quite a few limitations and several misrepresentations.
Vehicle Security Tips: How to Stay Off the ‘X’
Providing protective services requires a mind set that differs dramatically from the norm. This line of work demands a forward-thinking anticipation of what might occur and developing solutions on how to mitigate those risks. How does this differ from the norm? Half of the people on this planet are categorized into below average intelligence. Humor […]
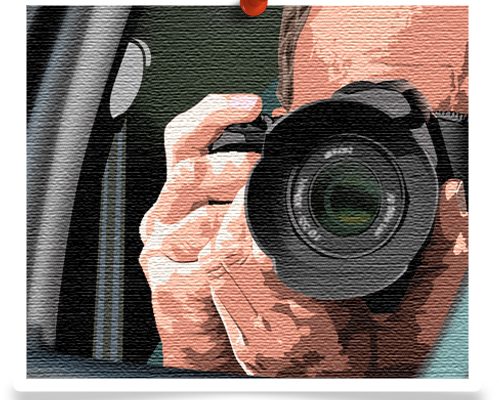
Choosing Camera Lenses for Surveillance
Choosing Camera Lenses for Surveillance is equally, if not more, important than choosing the camera body. Two of the most important considerations are the focal length and the speed.
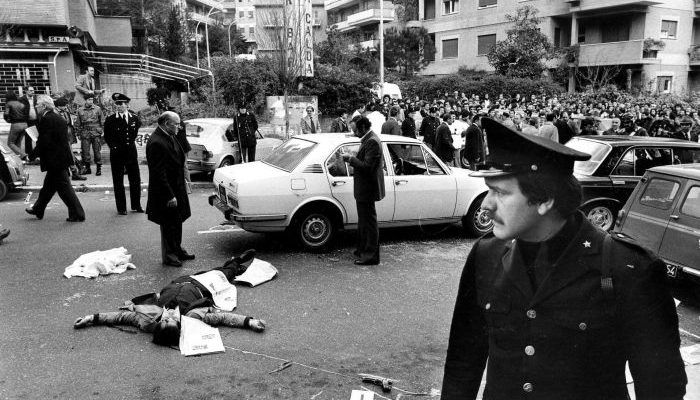
Surveillance Detection For Countering Terrorism
The ability to detect suspicious activity early in the planning phase is the primary means of defeating a terrorist attack. Thus, surveillance detection (SD) has become critical to successful intelligence collection, counter terrorism and security operations. By applying effective surveillance detection to security and counter terror operations we can effectively detect and prevent terrorist attacks in the planning phases, reduce the number of attacks and allow for safer operations in high risk environments.
Suited for Duty
When it comes to a wardrobe suited for duty, rule number one is, you don’t buy it, you acquire it over time. In most cases, unless you have unlimited resources this will be a slow build for most agents. To help you in developing a work-ready wardrobe I have put together a list of important considerations to help you get the essentials for good fit and function.
Hostile Surveillance Detection
Hostile surveillance detection is one of the few security techniques that preempts danger. As the name suggests it is the art of identifying an individual or group that is attempting to obtain intelligence by placing your client under surveillance. Its main advantage as a security tool is that it is proactive rather than reactive.
Surveillance Detection
Surveillance Detection A key skill for security and counter-terrorism professionals History has taught us that certain kinds of activities can indicate terrorist plans are in the works, especially when they occur at or near high profile or sensitive sites, places where high profile individuals reside or work, or where large numbers of people gather like […]
The Silent Witness & Hacking
The Silent Witness & Hacking With the proliferation of mobile phones in the public domain, many myths surround the actual truth that lies behind this wireless technology and the inappropriate use of the word Hacking associated with them in recent times. In my past role in a Police Technical Support Unit, I have interrogated […]
What's in your GO Bag – Going Digital
What’s in your GO Bag – Going Digital Your Principal has a known stalker that has sent letters and threatening emails. You are at a small venue for a public appearance, and suspect that they might show up. You need to remain with your client in a holding room, but what could make life […]